About
To make API calls in Kaltura, you need a Kaltura Session (KS) - a secure key that authenticates your requests. This guide walks you through how to create a KS using the Developer Console or TestMe Console. Once you have your KS, you can use it to interact with Kaltura’s API and manage your media programmatically.
Accessing the Kaltura APIs requires a Publisher Account. If you don't have such an account, see start a free Kaltura.com trial.
Via the Developer Console
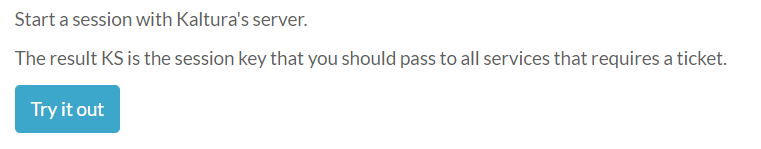
- Go to https://developer.kaltura.com/api-docs/service/session/action/start
- Click Try it out
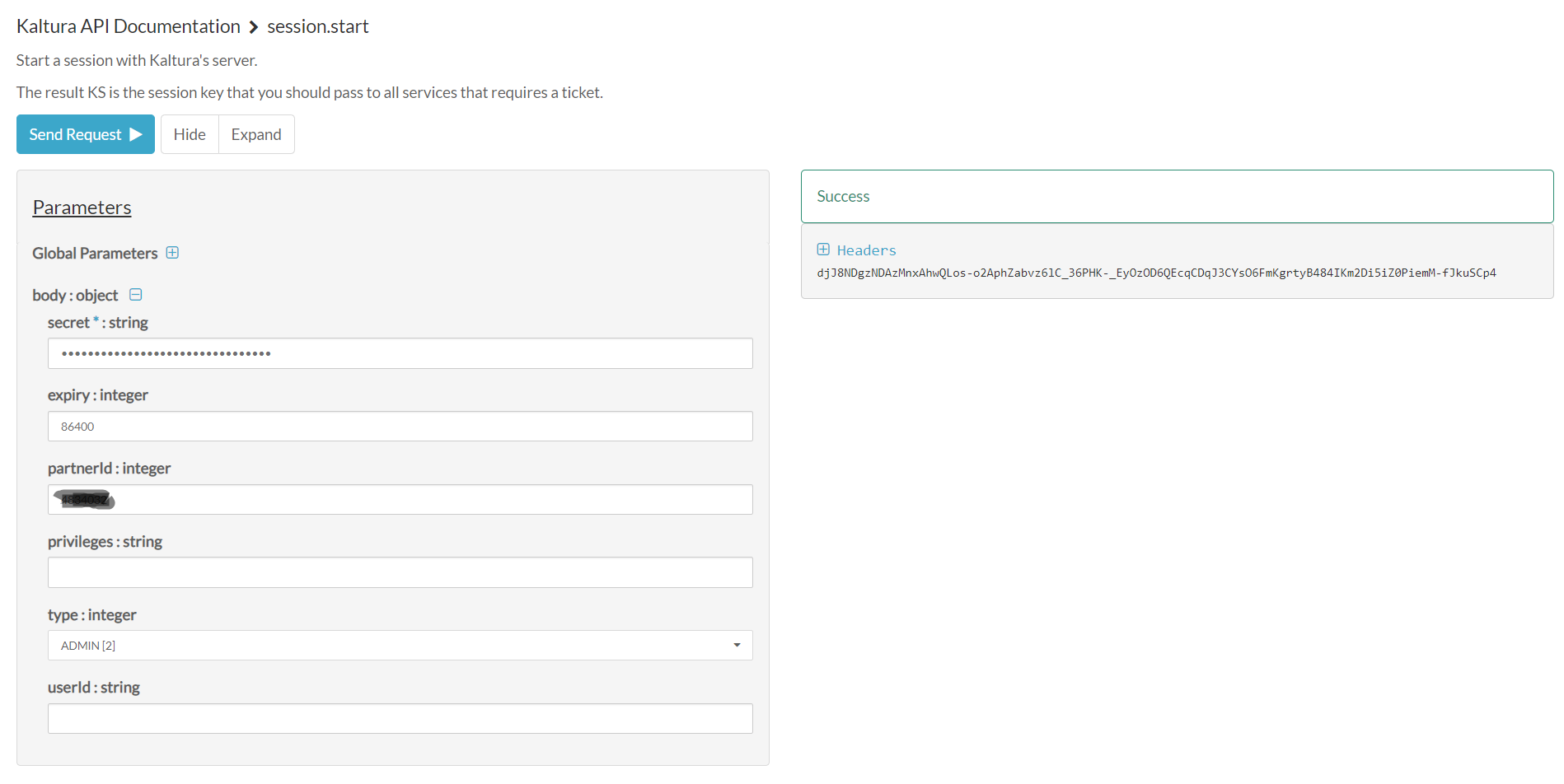
- Enter the Partner ID, Administrator Secret, and select type Admin.
Retrieve the Partner ID and Administrator Secret information from your Rich Media CMS application:- Click the Settings button and then Integration settings.
- Copy the following parameters:
A. Partner ID
B. Administrator Secret.
*The numbers and letters are different for each Partner.*
- Click Send Request. The KS string output is displayed on the right side.
Via the TestMe Console
- Go to: http://www.kaltura.com/api_v3/testme for US SaaS accounts or select the TestMe console by your region, such as:
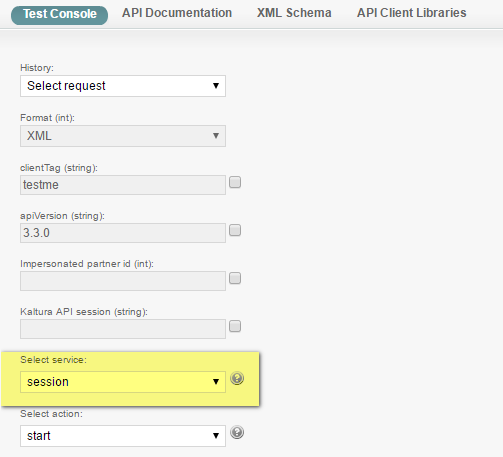
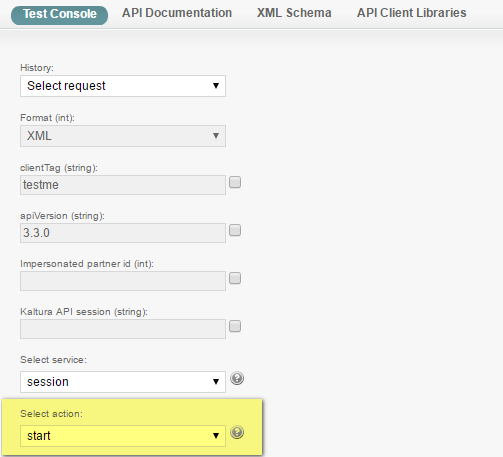
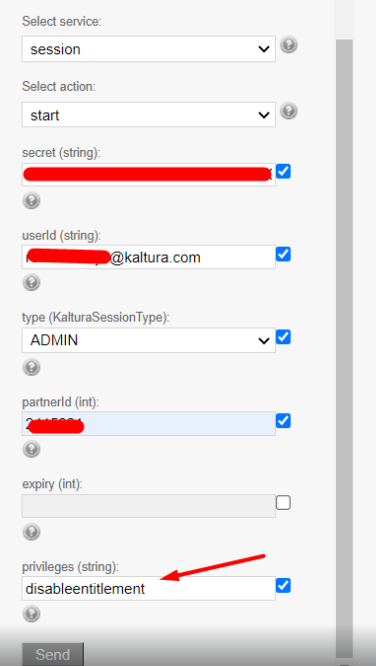
- Select Session from the Select Service drop-down list.
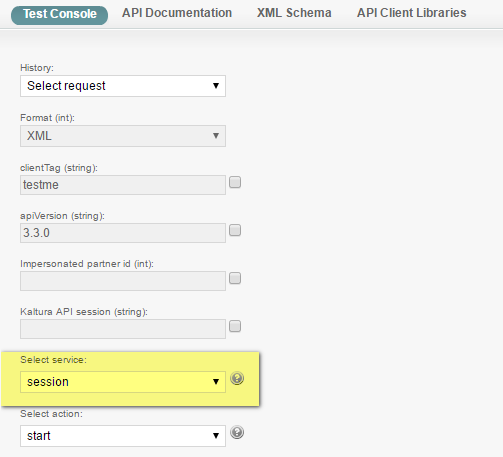
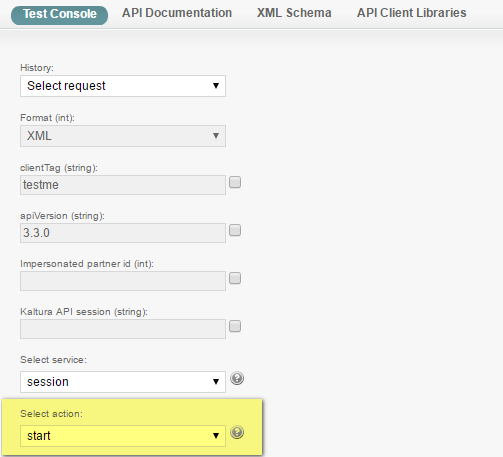
- Select Start from the Select action drop-down list.
Retrieve the Partner ID and Administrator Secret information from your Rich Media CMS application:
- Click the Settings button and then Integration settings.
- Copy the following parameters:
A. Partner ID
B. Administrator Secret.
*The numbers and letters are different for each Partner.*
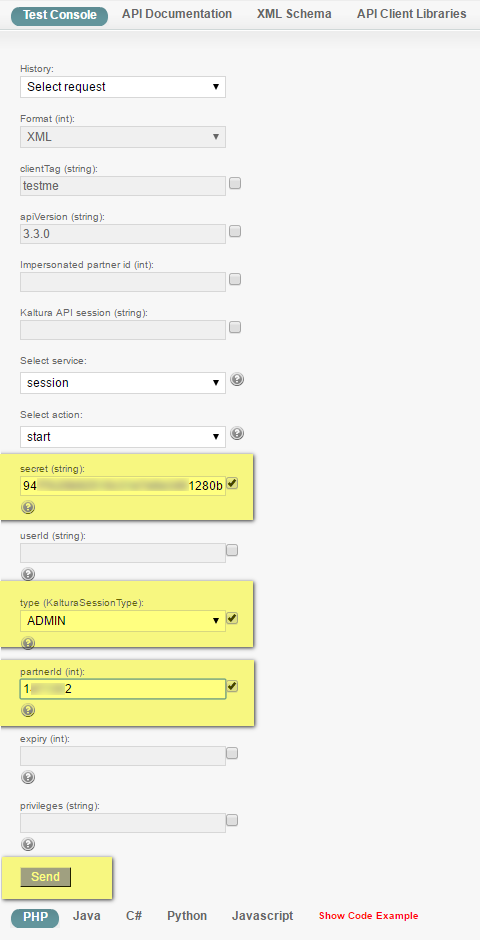
In the TestMe Console, paste the Partner ID and Administrator Secret information, and change the type field from USER to ADMIN.
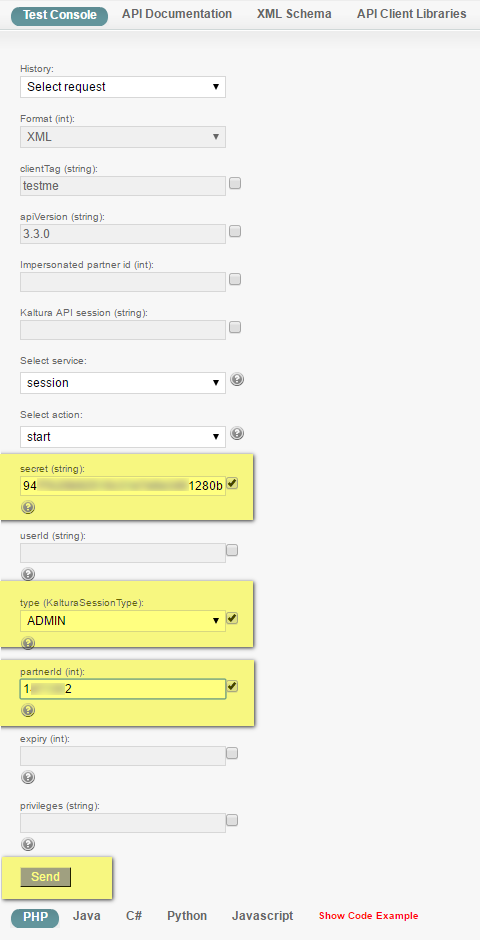
- Click Send.
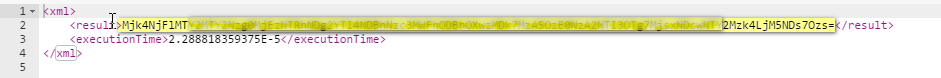
The output results should contain the KS, a Kaltura Session key.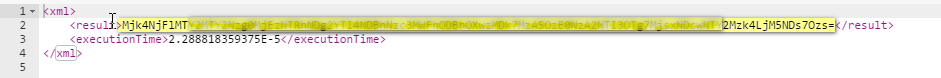
- Copy the KS string and put it in the Kaltura API session (string) field for your next API call.
That's it! Your API console is ready to make new API calls now.
If you notice that you cannot find all entries/categories in the API call output, this is likely to be related to the Default entitlements Enforcement
set on your account.
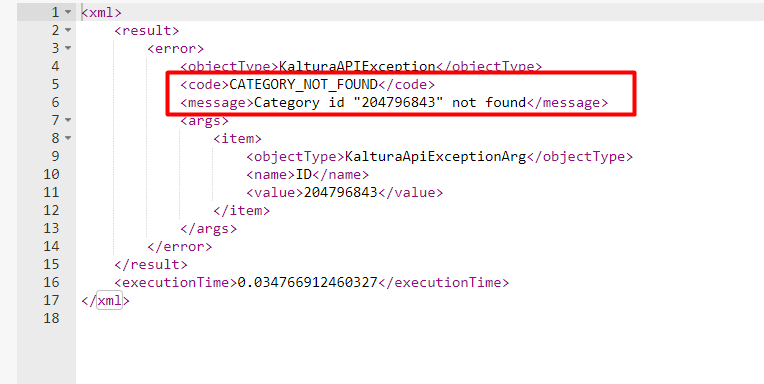 To accommodate this, you may set the ultimate privilege when generating the KS string and bypass this restriction.
To accommodate this, you may set the ultimate privilege when generating the KS string and bypass this restriction.
To do so, when generating the KS as described in this guide, please add the following string to the "privileges (string):" field:
all:*,disableentitlement .
Notes
The Kaltura API is REST based and stateless. Every call (request) made to the Kaltura API requires an authentication key, the Kaltura Session (aka KS), identifying the account on which the action is to be carried, the authenticated user and its role.
A Kaltura Session can be initiated in 3 different ways:
- Calling the session.start action, providing the account Partner ID and an Admin or User secret key.
$ks = $client->session->start ($adminSecret, $anyUserName, KalturaSessionType::ADMIN, $partnerId); $client->setKS($ks);
- Calling the user.loginByLoginId action, providing a User login ID (email), its Password and the account Partner ID.
$ks = $client->user->loginByLoginId($loginId, $password, $partnerId); $client->setKS($ks);
- Creating a session locally - Combine all the Kaltura Session details, and sign them using the shared secret.
$ks = $client->generateSession($adminSecret, $userId, $type, $partnerId); $client->setKS($ks);
The above examples are using the Kaltura PHP5 Client Library.
Important Security Notes:
ADMIN type KS provides super admin priveliges to the Kaltura account. If you're creating an application where the session will be exposed to the end-user, make sure that you are using a USER type KS and not ADMIN type. Exposing an ADMIN type KS in non-administrative context will expose your Kaltura account to risks of being used by malicious users with unrestricted access.
Sharing the account API secret keys with 3rd party vendors should be avoided, as secret keys can not be regenerated or blocked for access. Kaltura API based application developers and 3rd party application vendors should build their application to leverage the user.loginByLoginId API and ask the publisher for their email, password and account Id (aka partnerId). Users can be easily created, removed or blocked and their password can easily be changed.
To learn more about the KS and its usage read: Kaltura's API Authentication and Security: The Kaltura Session.